If you discover that your own website has been hacked, it initially comes as a shock for many of those affected, understandably. In order to minimize the damage to you and any consequential damage to third parties, there are a number of measures that affected website operators should take as soon as possible. Here is a summary of the most important actions Hostpoint recommends taking immediately:
What to do right away
- Certainly don’t do nothing
The worst thing you can do is do nothing at all. After all, this could have many grave consequences: This could infect unsuspecting website visitors or, in extreme cases, even harm the provider’s infrastructure and other customers. - Notify the responsible web hosting provider immediately
Providers like Hostpoint are always grateful when affected website operators notify them of hacking attacks. This enables them to ensure that no additional damage is caused to other websites or the hosting infrastructure. - Immediately stop all work on the website
The affected pages should either be taken offline by you, the webmaster or the provider. This is particularly important in the case of hacking attacks designed to spread malware. This protects unsuspecting website visitors from falling victim to the same attack themselves. - Scan devices for viruses and malware
Scan your own computers and mobile devices used to work on the website for viruses and malware and remove them. Unfortunately, hackers often install backdoors on the webmaster’s computer, for example, in order to attack the website (and other systems) again later. - Reset all passwords that have been used
Obviously, you need to change all passwords used for website administration. However, this may not be of much use if hackers gain access to different areas through back doors and can also view changed passwords right away. It is much more important after a hacking attack to change passwords wherever the same passwords have been used.

Other steps to remember
Once these immediate measures have been taken, the affected website operators can also take care of cleaning up the infected data or restoring the website. Here, too, Hostpoint recommends taking several specific measures:
- Clean up infected data
The infected pages, files and databases must be identified and cleaned up. A backup should only be restored once the method, time and gateway used for the attack have been identified. This information can then be used to determine which backup version to use as well. Be careful not to use antivirus programs installed locally on the computer. They are usually unable to fully detect and remove malware on a website. This also means that certain potentially dangerous elements simply cannot be detected (e.g. that a seemingly harmless link may conceal that it redirects to an infected website). - Data cleansing with professional help
It may be advisable to arrange for a specialized professional provider to clean up the website data. Not all website operators are experienced enough to carry out the necessary clean-up steps on their own. There is a risk of something being overlooked, which could allow hackers to attack again. - Restore backups
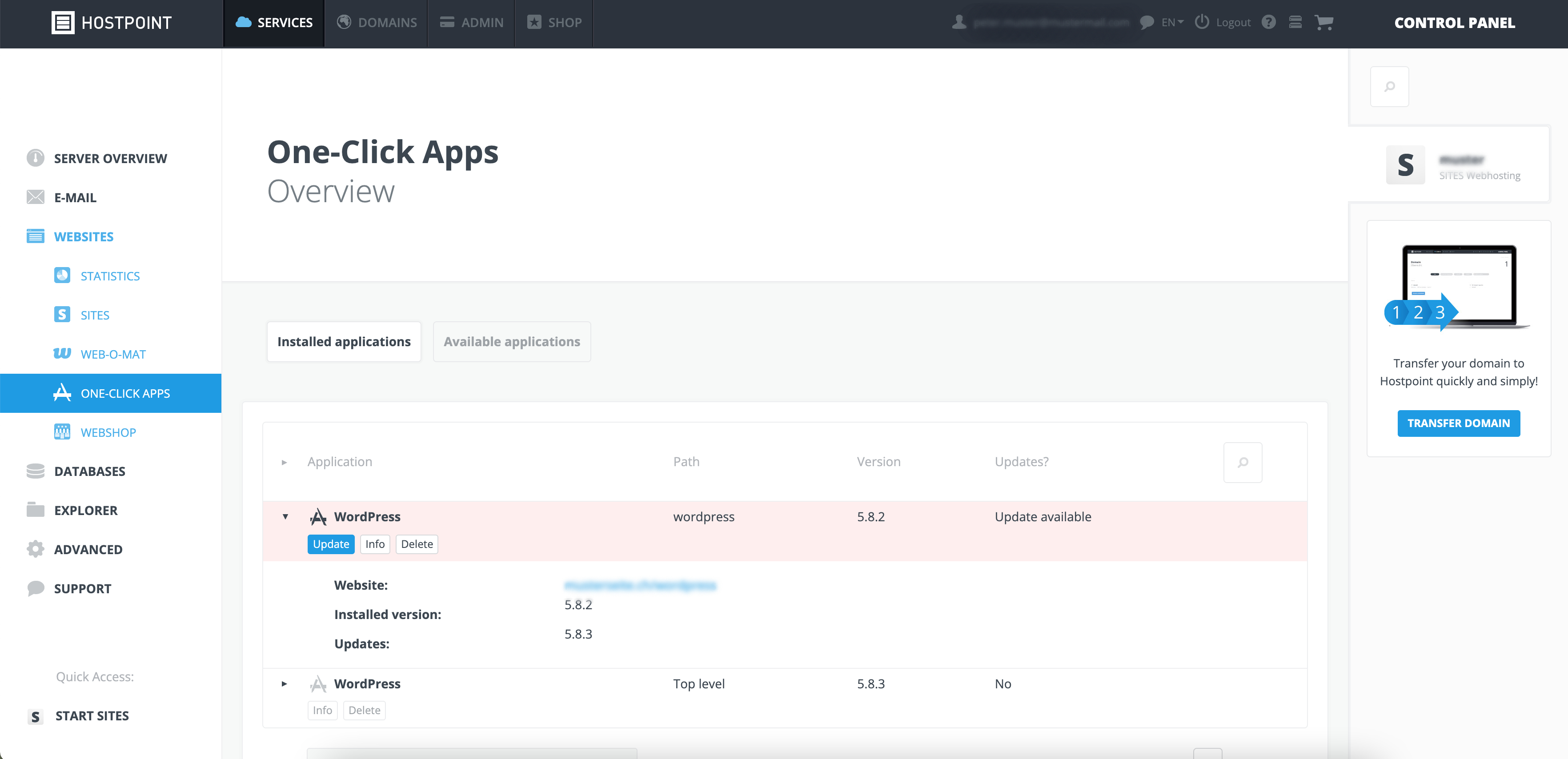
The affected parties can restore backups created by customers themselves or with the help of their web hosting provider (Hostpoint charges a flat fee of CHF 100 for this). However, it is important that backups are performed in a secure environment. Installing a backup on an infected web server is of little use. Care should also be taken to ensure that no infected files and databases are reused during the restore process. You can find more information about this in our Support Center. - Updating the CMS and plug-ins
Once the hacked website version is deleted, the backup is restored and all passwords are reset, you should install all available updates for the CMS, plug-ins and themes. We recommend completely removing all unnecessary elements, such as plug-ins, files, etc. and scanning for additional malware. In addition, installing CMS firewalls may prevent future attacks. - Comply with any required reporting obligations
If it can be assumed that personal data has been accessed and stolen by the hackers following an attack, this may need to be reported to the authorities, for example, in the case of websites subject to the European General Data Protection Regulation (GDPR). - Report to the National Cyber Security Centre
To help combat cybercrime in general, it is a good idea to report a hacking incident to the National Cyber Security Centre (NCSC). The NCSC has set up an easy-to-use reporting page for this purpose here: https://www.report.ncsc.admin.ch/en/.
What is Hostpoint doing to protect me and my website?
Hostpoint attaches great importance to the security of its own infrastructure and the websites of its customers. That’s why we use a range of security measures and systems to effectively protect our customers.
We maintain our own top-quality, high-performance web hosting infrastructure that meets the highest security standards. Year after year, Hostpoint invests millions in maintaining and expanding its infrastructure while also continuing to develop its server software. In addition, Hostpoint’s infrastructure has protections in place to guard against DDoS attacks and certain protective mechanisms to automatically detect and, if possible, defend against attacks.
Customer data is backed up several times a day (going back up to 180 days depending on the product). Hostpoint also takes hourly snapshots of the last 24 hours. All data is stored at a high-grade data center certified for banking and operated by Interxion in Switzerland.
Regular maintenance and updates are key
Nevertheless, it is mainly the responsibility of the website operator or customers themselves to protect against hacking. Those who fail to regularly install the necessary and available security for their websites will be at greater risk. We have put together a few practical rules and recommended actions that every website operator should take to heart:
- The issue of security should be given sufficient attention from the outset.
- Regular updates (at least weekly) to the CMS and the connected applications are not a necessary evil but rather are the basis for secure website operation. Some plug-ins even have automatic update features.
- Only use plug-ins or themes that have been published or at least verified by the respective CMS vendor. Free software from third-party sites should be used with caution, as these are often pirated copies and may also contain malware.
- Plug-ins that are no longer in use should be disabled or removed completely from the web server.
- Test websites that are no longer in operation should also be deleted. In general, it is a good idea to include upstream password protection on test or staging pages.
- Remove old or unused CMS administrator accounts.
- Responsible use of passwords is very important. Logins should not be used by multiple people. Do not use password lists saved in Excel files or similar. Instead, use password managers (key ring systems).
- Likewise, passwords should never be used in more than one system and should be sufficiently complex (combinations of letters, numbers and special characters as well as sufficient length).
- Enable and use two-factor authentication for logins whenever possible.
- Hostpoint creates backups for customers for a period going back up to 180 days (depending on the product). Nevertheless, we also recommend that you regularly create your own backups for website data and databases (locally or in the cloud).
There are other precautions as well, such as using computers and web browsers that are regularly updated, current anti-virus software and firewalls, website and file system monitoring and encrypted data transmission via SFTP.
Info
You can find more helpful information in our Support Center and on the websites of the National Cyber Security Centre (NCSC), the Swiss Crime Prevention organization (SKP) or visit the Swiss Internet Security Alliance (iBarry) for more helpful tips on preventing cyberattacks.
You can report hacking incidents via the NCSC by going to the following web address: https://www.report.ncsc.admin.ch/en/
Security precautions are no guarantee for security
Unfortunately, there is no such thing as complete protection against hacking attacks. With what are known as zero-day exploits, hackers ruthlessly exploit vulnerabilities as soon as they are discovered. If, for example, a security vulnerability crops up in a plug-in used on your website, it is unfortunately possible that hackers will exploit this vulnerability before the developers responsible for the software even become aware of it. Nevertheless, the precautions described above (particularly regular updates) are the best way to minimize the likelihood of a hacking attack.
If you want to bother with the issue of security as little as possible, you can assign this task to a webmaster or a digital agency, for example. Or you can opt for Software-as-a-Service (SaaS) solutions like Hostpoint’s Sites and Webshop products. For products like these, the web hosting provider – in this case Hostpoint – manages security and maintenance tasks, such as monitoring and installing updates.























































