Unfortunately, there are probably hardly any hosting customers who have not received a phishing e-mail at some point. Fortunately, most users do not fall for the fraudulent scams, but since there are always people affected, it is worth taking a closer look at the issue.
Phishing is – to the chagrin of many users and companies – a very common form of cybercrime. In most cases, phishing attacks are carried out via e-mail (but often also via electronic short messages or telephone calls). The attackers’ goal is to impersonate trustworthy service providers in order to obtain login data, passwords, addresses or even payment information such as credit card details.
For example, a user receives an e-mail from a sender posing as a known parcel delivery service. In it, the recipient is informed that a parcel delivery is waiting for them and that they still have to pay a fee for the delivery. However, clicking on a link in the e-mail takes the user to a fake website. Once the user fills in the required information and makes the payment, personal data and payment information fall into the hands of the fraudsters. This is a very common form of phishing attempt.
Fishing for personal data
The term phishing derives from the word “fishing”. Phishing first appeared in the nineties from the internet service provider AOL. Attackers impersonated AOL administrators in e-mails and chats to gain access to users’ login data and user accounts. Since then, phishing cases have increased sharply from year to year. Today, they affect a wide variety of industries and cause billions of dollars in economic damage worldwide. Combined with other forms of cybercrime, global cybercrime losses in 2021 are expected to reach over 6 trillion US dollars. This value is expected to grow to over 10.5 trillion annually by 2025.
The web hosting industry – along with credit card companies, parcel delivery services and telecom providers, for example – is also, unfortunately, the target of downright phishing waves time and again, because domain names and the associated e-mail addresses on the corresponding websites are often public and thus relatively easy to access. Hostpoint customers receive numerous examples of phishing e-mails, stating that credit card information supposedly needs to be updated, that their Hostpoint ID needs to be restored or that their domain is about to expire and needs to be paid within a very short deadline.
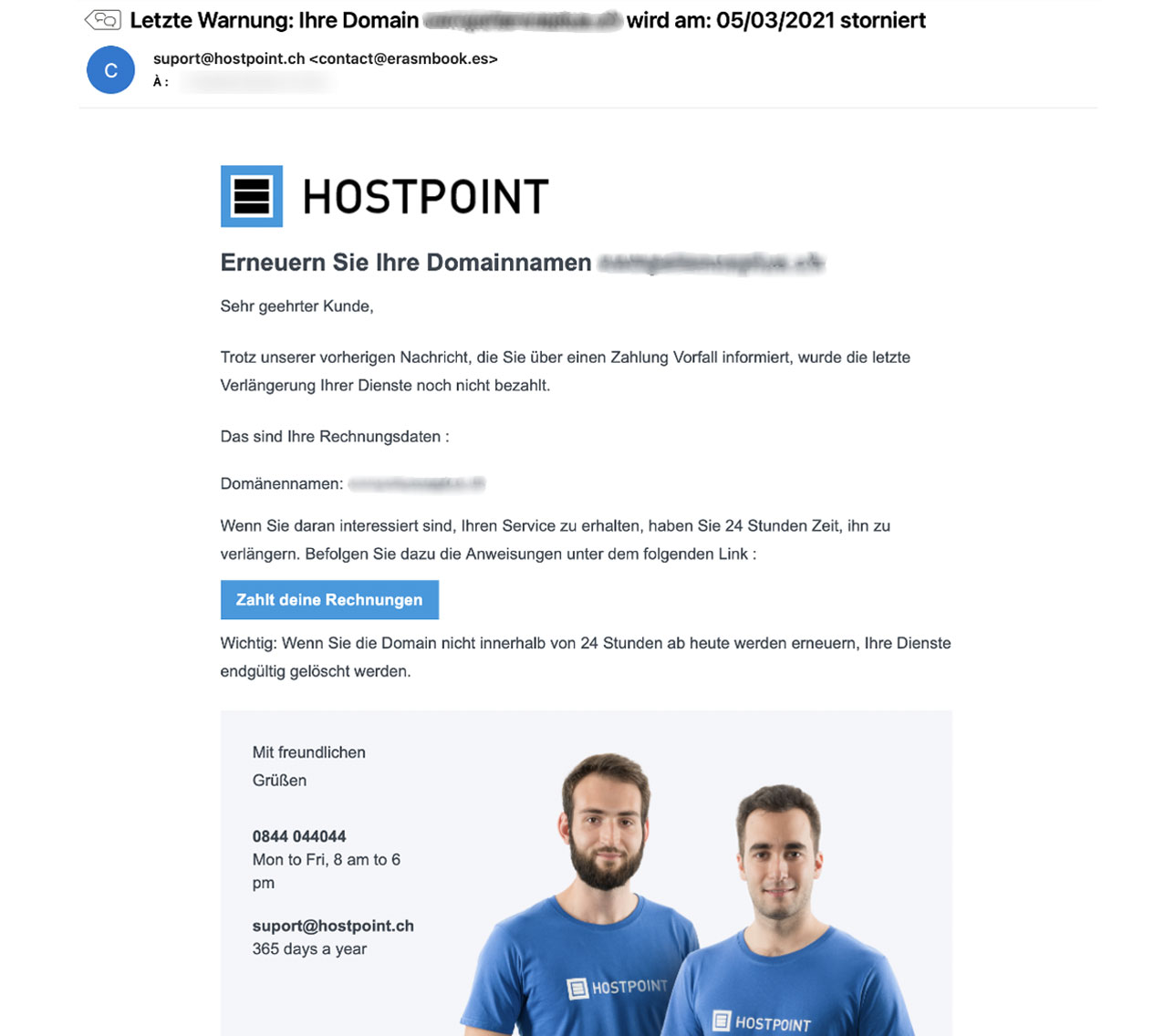
In recent years, phishing e-mails have become significantly more professional-looking. The e-mails are becoming more and more sophisticated and are often hard to distinguish from legitimate Hostpoint e-mails at first glance.
Often, attackers do not even target users’ personal data directly but try to gain access to their hosting accounts via phishing. These are then misused to send further phishing or spam e-mails, for example.
Be alert for warning signs and rules
Since today’s phishing e-mails are increasingly sophisticated in structure and design, it is not always easy to recognize them as scams. But there are some characteristics for which phishing attempts can be recognized:
- In the subject lines, title or text of phishing e-mails, the user is asked to take immediate action in an attempt to put pressure on them;
- The scam e-mails give recipients very short deadlines (e.g. 24, 48 or 72 hours) for supposedly outstanding payments;
- On closer inspection, the sender’s e-mail address does not correspond to the domain of the supposed service provider (e.g. does not contain “@hostpoint.ch”);
- Hyperlinks integrated in the mail show a different URL than the one actually hidden behind it. You can often check this by hovering your mouse over the link before clicking on it;
- Very often, phishing e-mails contain many spelling mistakes, wildly placed special characters or even changing languages in the text.
Hostpoint regularly draws customers’ attention to the dangers of phishing and recommends that they always observe the following rules:
- Never allow yourself to be put under pressure. Hostpoint will never demand disproportionately short payment periods;
- Check the destination address of links before clicking on them;
- If in doubt, do not provide passwords or personal information;
- If in doubt, do not make any payments, first go to the Hostpoint Control Panel to check whether there are any outstanding invoices;
- Activate two-factor authentication for logging into the Hostpoint Control Panel. Read more here.
- Delete e-mails detected as phishing immediately. Evidence of suspected phishing attempts can be forwarded to phishing-report@hostpoint.ch weitergeleitet werden.
Tilting at windmills is not futile
Hostpoint puts a lot of effort into combating phishing. While the hosting and e-mail infrastructure is continuously optimized and better secured on the technical side, any phishing sites found to be posing as Hostpoint or other companies and institutions are blocked as promptly as possible. Phishing cases are also reported to the National Cyber Security Center (formerly MELANI) via the anti-phishing site.
Unfortunately, it is difficult to prosecute against phishing because attackers often hide behind proxy services abroad or misuse hacked servers to spread their scams. The National Cyber Security Center, die Swiss Crime Prevention organization and the Swiss Internet Security Alliance (iBarry), however, undertake regular public education work to raise awareness among internet users about the dangers of phishing and other forms of cybercrime.
Phishing is a major annoyance for users as well as hosting providers like Hostpoint but fortunately only very few fall for the scam attempts. And, thanks to the many valuable efforts of providers, authorities, companies and other organizations, the fight against phishing and other forms of cybercrime is by no means futile, especially in this country. Public awareness of phishing is increasing, customers are becoming more cautious on their own initiative, and acceptance of additional security measures is now very high.
Learn more about phishing and how you can recognize fraudulent e-mails on the Hostpoint Phishing Info Page.























































